Endpoint Protection Services: Safeguarding Your Digital Frontier
In today’s interconnected world, where businesses rely heavily on technology and individuals are constantly connected, the need for robust cybersecurity measures has never been greater. With cyber threats becoming more sophisticated and prevalent, it is essential to have effective endpoint protection services in place to safeguard your digital assets.
Endpoint protection services refer to a comprehensive approach to securing all endpoints within a network. Endpoints include devices such as laptops, desktops, servers, mobile phones, and even IoT (Internet of Things) devices. These endpoints are often the entry points for cybercriminals seeking unauthorized access or attempting to exploit vulnerabilities.
The primary goal of endpoint protection services is to prevent, detect, and respond to various types of cyber threats that may target these endpoints. This includes malware attacks, ransomware incidents, phishing attempts, data breaches, and other malicious activities.
One of the key components of endpoint protection services is antivirus software. This software acts as a shield against known malware by scanning files and applications for any signs of malicious code. It also regularly updates its virus definitions to stay ahead of emerging threats.
However, modern endpoint protection services go beyond traditional antivirus software. They incorporate advanced features such as real-time threat intelligence, behavioral analysis, machine learning algorithms, and artificial intelligence capabilities. These technologies enable proactive threat detection by identifying suspicious patterns or anomalies in user behavior or network traffic.
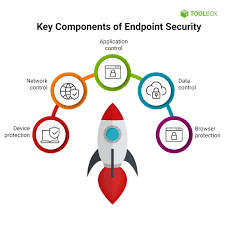
Endpoint protection services also include features like firewall management, intrusion detection and prevention systems (IDPS), data loss prevention (DLP), encryption tools, vulnerability assessments, and patch management. These additional layers of security help fortify the overall defense posture against potential attacks.
Furthermore, many endpoint protection services offer centralized management consoles that allow IT administrators to monitor and control all endpoints from a single interface. This simplifies the task of deploying updates or security policies across the network while providing visibility into potential vulnerabilities or ongoing threats.
For businesses operating in highly regulated industries or dealing with sensitive customer data, endpoint protection services are particularly crucial. Compliance requirements, such as GDPR (General Data Protection Regulation) or HIPAA (Health Insurance Portability and Accountability Act), demand robust security measures to protect confidential information. Endpoint protection services provide the necessary security controls and reporting capabilities to meet these compliance standards.
In conclusion, endpoint protection services play a vital role in safeguarding our digital frontier. By employing a multi-layered approach to cybersecurity, these services protect endpoints from various threats and provide peace of mind for both individuals and businesses. In an ever-evolving threat landscape, investing in reliable endpoint protection services is a proactive step towards ensuring the safety and integrity of our digital lives.
6 Essential Tips for Effective Endpoint Protection Services
- Ensure that your endpoint protection service is regularly updated with the latest security patches and antivirus definitions.
- Use a multi-layered approach to endpoint protection, such as firewalls, anti-malware programs, and host intrusion prevention systems (HIPS).
- Consider using a cloud-based solution for your endpoint protection services to ensure maximum coverage of all devices connected to your network.
- Monitor all endpoints for suspicious activity and respond quickly when threats are detected.
- Utilise encryption technology on endpoints to protect sensitive data from being accessed by unauthorised users or malicious actors.
- Train employees on best security practices such as using strong passwords and avoiding clicking links in emails from unknown sources
Ensure that your endpoint protection service is regularly updated with the latest security patches and antivirus definitions.
Endpoint Protection Services: The Importance of Regular Updates
In the ever-changing landscape of cybersecurity, staying one step ahead of malicious actors is crucial. One key tip to ensure the effectiveness of your endpoint protection service is to regularly update it with the latest security patches and antivirus definitions.
Endpoint protection services, including antivirus software, rely on up-to-date information about emerging threats and vulnerabilities. Security patches are released by software vendors to address known vulnerabilities in their products. By keeping your endpoint protection service updated with these patches, you can close potential security gaps that cybercriminals may exploit.
Similarly, antivirus definitions are files that contain information about known malware and viruses. They help the endpoint protection software identify and block malicious code from infecting your devices. However, new threats emerge daily, requiring constant updates to keep pace with evolving malware variants. By regularly updating your antivirus definitions, you enhance your endpoint protection’s ability to detect and prevent the latest threats.
Failing to update your endpoint protection service can leave your devices vulnerable to attacks. Cybercriminals are constantly developing new techniques to bypass outdated security measures. Without regular updates, your endpoint protection may not be equipped to defend against these emerging threats effectively.
Fortunately, most modern endpoint protection services offer automatic updates or provide notifications when new patches or antivirus definitions are available. It is essential to enable these features and ensure that they are functioning correctly. Regularly check for updates manually if necessary or set up automated schedules for updates.
By prioritizing regular updates for your endpoint protection service, you strengthen your defense against cyber threats significantly. It’s a simple yet effective practice that can save you from potential data breaches, ransomware attacks, or other malicious activities.
Remember that cybersecurity is an ongoing process rather than a one-time task. Threats evolve rapidly, and so should our defensive measures. Make it a habit to check for updates regularly and encourage others in your organization or household to do the same.
In conclusion, ensuring that your endpoint protection service is regularly updated with the latest security patches and antivirus definitions is a vital step in maintaining a robust cybersecurity posture. By doing so, you enhance your protection against emerging threats and reduce the risk of falling victim to cyberattacks. Stay vigilant, stay updated, and stay secure.
Use a multi-layered approach to endpoint protection, such as firewalls, anti-malware programs, and host intrusion prevention systems (HIPS).
Enhancing Endpoint Protection: The Power of a Multi-Layered Approach
In the ever-evolving landscape of cybersecurity threats, relying on a single layer of defense is no longer sufficient to protect your valuable digital assets. To fortify your endpoint protection, it is crucial to adopt a multi-layered approach that combines various security measures. This article explores the effectiveness of using firewalls, anti-malware programs, and host intrusion prevention systems (HIPS) as part of this comprehensive strategy.
Firewalls act as the first line of defense by monitoring and controlling incoming and outgoing network traffic. They create a barrier between your internal network and external sources, filtering out potentially malicious connections. By enforcing access control policies and examining packets for suspicious activity, firewalls significantly reduce the risk of unauthorized access or data breaches.
Anti-malware programs are another essential component in endpoint protection. These software solutions detect, block, and remove various types of malware that may attempt to infiltrate your devices or networks. They continuously scan files, applications, emails, and web traffic to identify any signs of malicious code. With regular updates to their virus definitions, anti-malware programs stay up-to-date with emerging threats.
Host Intrusion Prevention Systems (HIPS) provide an additional layer of security by monitoring system activities and behaviors for any signs of unauthorized or malicious actions. HIPS use advanced techniques such as anomaly detection and behavior analysis to identify potentially harmful activities that may go unnoticed by traditional antivirus software. By actively blocking or alerting against suspicious behavior in real-time, HIPS can prevent potential attacks before they cause significant damage.
By combining firewalls, anti-malware programs, and HIPS within your endpoint protection strategy, you create multiple layers of defense that work together synergistically. Each layer adds an extra level of scrutiny to ensure comprehensive protection against a wide range of cyber threats.
Implementing a multi-layered approach not only increases the chances of detecting and blocking malicious activities but also reduces the risk of false positives or false negatives. Different security measures excel in different areas, and by leveraging their strengths collectively, you create a more robust defense against potential vulnerabilities.
It’s important to note that while a multi-layered approach significantly enhances endpoint protection, it should be complemented by regular software updates, patch management, user education on cybersecurity best practices, and strong password policies. These additional measures further strengthen your overall security posture.
In conclusion, adopting a multi-layered approach to endpoint protection is vital in today’s threat landscape. By combining firewalls, anti-malware programs, and HIPS, you establish a powerful defense mechanism that significantly reduces the risk of cyberattacks. Stay one step ahead of cybercriminals by fortifying your endpoints with multiple layers of security.
Consider using a cloud-based solution for your endpoint protection services to ensure maximum coverage of all devices connected to your network.
Consider Using a Cloud-Based Solution for Enhanced Endpoint Protection
In today’s digital landscape, where businesses and individuals rely heavily on interconnected devices, securing endpoints is of paramount importance. Endpoint protection services are essential for safeguarding these devices from cyber threats. One effective tip to enhance your endpoint protection strategy is to consider using a cloud-based solution.
A cloud-based endpoint protection service offers numerous advantages over traditional on-premises solutions. By leveraging the power of the cloud, you can ensure maximum coverage and protection for all devices connected to your network, regardless of their physical location.
One key benefit of a cloud-based approach is its scalability. As your business grows or as you add more devices to your network, a cloud-based solution can easily accommodate the increased demand without requiring additional hardware or infrastructure investments. This flexibility allows you to scale up or down as needed, ensuring that all endpoints are adequately protected.
Additionally, a cloud-based endpoint protection service provides real-time updates and threat intelligence. With cyber threats evolving rapidly, it is crucial to have the latest security measures in place. Cloud solutions have the advantage of receiving continuous updates and patches from security experts who monitor emerging threats worldwide. This ensures that your endpoints are protected against the most recent malware strains and vulnerabilities.
Another advantage of a cloud-based approach is centralized management. With a cloud console, you can easily monitor and manage all endpoints from a single interface, regardless of their physical location. This simplifies administration tasks such as deploying updates or implementing security policies across multiple devices. It also provides comprehensive visibility into potential vulnerabilities or ongoing threats across your entire network.
Cloud-based endpoint protection services also offer enhanced resilience and disaster recovery capabilities. In case of an incident or hardware failure at one location, your data remains secure in the cloud and accessible from other devices or locations. This redundancy ensures business continuity even in challenging situations.
Furthermore, by opting for a cloud-based solution, you alleviate the burden on internal IT resources. The cloud provider takes care of infrastructure maintenance, software updates, and security patches, allowing your IT team to focus on other critical tasks. This not only saves time and effort but also ensures that your endpoint protection remains up to date without any administrative overhead.
In conclusion, considering a cloud-based solution for your endpoint protection services can provide significant benefits in terms of scalability, real-time updates, centralized management, resilience, and resource optimization. By embracing the cloud, you can ensure maximum coverage and protection for all devices connected to your network, regardless of their physical location. Stay one step ahead of cyber threats by harnessing the power of the cloud for your endpoint protection needs.
Monitor all endpoints for suspicious activity and respond quickly when threats are detected.
Endpoint Protection Services: The Importance of Monitoring and Swift Response
In the ever-changing landscape of cybersecurity, one crucial tip for effective endpoint protection services is to monitor all endpoints for suspicious activity and respond quickly when threats are detected. This proactive approach can make a significant difference in preventing potential data breaches, malware infections, or other malicious activities.
Monitoring all endpoints within a network allows IT administrators to keep a close eye on user behavior, network traffic, and system activities. By continuously monitoring these endpoints, any unusual or suspicious activity can be swiftly identified and investigated. This includes detecting unauthorized access attempts, unusual file transfers, or abnormal system behavior.
The key to successful endpoint protection lies in the ability to respond quickly once a threat is detected. Time is of the essence when it comes to mitigating potential risks and minimizing the impact of an attack. A swift response can prevent further compromise of sensitive data or the spread of malware across the network.
When a threat is detected, endpoint protection services should have automated response mechanisms in place to take immediate action. This could involve isolating infected endpoints from the network, blocking suspicious IP addresses or domains, terminating malicious processes, or quarantining compromised files.
Additionally, it is important to have incident response procedures defined in advance. These procedures outline the steps to be taken when a threat is identified and ensure that there is a coordinated effort among IT teams to mitigate risks effectively. This includes notifying relevant stakeholders, documenting the incident for future analysis and improvement, and implementing any necessary remediation measures.
By monitoring all endpoints for suspicious activity and responding swiftly when threats are detected, businesses can significantly enhance their security posture. This proactive approach minimizes the window of opportunity for cybercriminals and reduces the potential impact of an attack.
Moreover, continuous monitoring allows organizations to gather valuable insights into emerging threats and vulnerabilities within their networks. By analyzing patterns and trends in endpoint activity, security teams can identify potential weaknesses or gaps in their defense strategies and take proactive measures to address them.
In conclusion, monitoring all endpoints for suspicious activity and responding quickly to threats is a fundamental aspect of effective endpoint protection services. By staying vigilant and taking immediate action, businesses can fortify their security defenses, protect sensitive data, and mitigate the risks associated with today’s evolving cyber threats.
Utilise encryption technology on endpoints to protect sensitive data from being accessed by unauthorised users or malicious actors.
Endpoint Protection Tip: Harness the Power of Encryption to Safeguard Sensitive Data
In today’s digital landscape, where data breaches and cyber attacks are on the rise, protecting sensitive information has become paramount. One effective way to fortify your endpoint protection strategy is by leveraging encryption technology on your endpoints.
Encryption acts as a powerful shield, rendering data unreadable to unauthorized users or malicious actors who may gain access to your endpoints. By encrypting sensitive data, you add an extra layer of security that ensures confidentiality and prevents unauthorized disclosure.
When implemented correctly, encryption technology scrambles data using complex algorithms, making it virtually impossible for anyone without the decryption key to decipher the information. This means that even if someone manages to intercept or steal the encrypted data, they won’t be able to make sense of it without the proper credentials.
By utilizing encryption on your endpoints, you can protect a wide range of sensitive information. This includes personally identifiable information (PII) such as names, addresses, and social security numbers, financial data like credit card details or bank account numbers, confidential business documents or trade secrets, and any other critical information that could cause harm if accessed by unauthorized individuals.
Implementing encryption technology on endpoints is relatively straightforward. Many modern operating systems offer built-in encryption tools that allow you to encrypt specific files or entire disk drives. Additionally, there are third-party encryption software solutions available that offer more advanced features and centralized management capabilities for larger organizations.
It’s important to note that encryption should be used in conjunction with other endpoint protection measures for maximum effectiveness. This includes employing strong authentication methods like multi-factor authentication (MFA), regularly updating software and security patches on endpoints, implementing robust antivirus software with real-time threat detection capabilities, and educating end-users about best practices for data protection.
Remember that while encryption provides a significant layer of security, it does not guarantee absolute invulnerability. It is essential to regularly review and update your encryption protocols to stay ahead of emerging threats and vulnerabilities. Additionally, maintaining secure backups of your encrypted data ensures that you can recover your information in case of any unforeseen incidents.
In conclusion, leveraging encryption technology on your endpoints is an essential step in protecting sensitive data from unauthorized access. By implementing encryption measures alongside other endpoint protection strategies, you can significantly enhance the security posture of your organization or personal devices. Stay one step ahead of cyber threats by harnessing the power of encryption and safeguarding your valuable information from falling into the wrong hands.
Train employees on best security practices such as using strong passwords and avoiding clicking links in emails from unknown sources
The Importance of Employee Training in Endpoint Protection Services
When it comes to safeguarding your organization’s digital assets, investing in robust endpoint protection services is essential. However, even the most advanced security solutions can be compromised if employees are not adequately trained on best security practices. One crucial tip for enhancing endpoint protection is to educate employees on the importance of using strong passwords and avoiding clicking links in emails from unknown sources.
Passwords act as the first line of defence against unauthorized access to sensitive information. Weak or easily guessable passwords can leave endpoints vulnerable to attacks. By training employees on creating strong passwords, such as using a combination of letters, numbers, and special characters, you can significantly reduce the risk of password-related breaches.
In addition to strong passwords, it is vital to emphasize the importance of not sharing passwords across different accounts or with colleagues. Encouraging employees to use unique passwords for each account adds an extra layer of protection against potential credential-based attacks.
Another common method cybercriminals use to gain unauthorized access or distribute malware is through phishing emails. These deceptive emails often appear legitimate and trick users into clicking malicious links or providing sensitive information. By training employees on how to identify phishing emails and avoid clicking suspicious links from unknown sources, you can minimize the risk of falling victim to these types of attacks.
Educating employees about common signs of phishing emails, such as spelling errors, unexpected attachments, or urgent requests for personal information, helps them recognize potential threats. Encourage them to verify the legitimacy of any email before clicking on links or downloading attachments by contacting the sender directly using a known contact method.
Regularly conducting training sessions and providing resources like posters or email reminders can reinforce these best security practices among your workforce. Additionally, consider implementing simulated phishing exercises that allow employees to practice identifying and reporting potential phishing attempts in a safe environment.
By prioritizing employee training in endpoint protection services, you empower your workforce as an active line of defense against cyber threats. Strong passwords and cautious email practices significantly reduce the risk of successful attacks, ultimately enhancing the overall security posture of your organization’s endpoints.
Remember, cybersecurity is a collective effort, and every employee plays a crucial role in maintaining a secure digital environment. By fostering a culture of security awareness and providing ongoing training, you can create a workforce that is well-equipped to protect your organization’s valuable data and assets from the ever-evolving landscape of cyber threats.