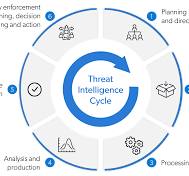
Securing Your Network: The Power of Network Security Appliances
Enhancing Cybersecurity with Network Security Appliances Enhancing Cybersecurity with Network Security Appliances In today's digital…
0 Comments