Endpoint Protection: Safeguarding Your Digital Frontline
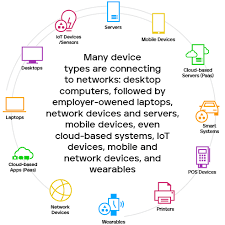
In today’s increasingly interconnected world, the security of our digital devices and data has become paramount. With cyber threats evolving at an alarming rate, it is crucial to have robust measures in place to protect our endpoints – the devices we use every day, such as laptops, smartphones, and tablets. This is where endpoint protection comes into play.
Endpoint protection refers to a comprehensive security solution designed to safeguard these vulnerable endpoints from a wide range of threats, including malware, ransomware, phishing attacks, and zero-day exploits. It acts as a frontline defence mechanism, shielding your devices and data from potential harm.
So, what makes endpoint protection so essential? Let’s delve deeper into its key features and benefits:
- Multi-layered Protection: Endpoint protection employs multiple layers of defence mechanisms to provide comprehensive security coverage. These layers include antivirus scanning, firewall protection, intrusion detection systems (IDS), behavioural analysis, application control, web filtering, and more. By combining these elements, endpoint protection ensures that potential threats are detected and neutralized before they can cause harm.
- Real-time Threat Intelligence: To stay ahead of emerging threats in the ever-changing cybersecurity landscape, endpoint protection solutions rely on real-time threat intelligence. By continuously monitoring global threat feeds and analyzing patterns and behaviours across various endpoints worldwide, these solutions can identify new malware strains and attack vectors promptly. This proactive approach allows for early detection and mitigation of potential risks.
- Centralized Management: Endpoint protection solutions often come with centralized management consoles that allow administrators to monitor and manage security policies across all connected devices from a single interface. This centralized approach streamlines security operations by enabling efficient deployment of updates and patches while providing real-time visibility into the overall security posture of the network.
- Data Loss Prevention (DLP): Endpoint protection goes beyond just detecting threats; it also helps prevent data breaches by implementing data loss prevention measures. DLP features ensure that sensitive data is encrypted, restrict unauthorized access, and monitor the transfer of confidential information, both within and outside the network. This helps organizations comply with data protection regulations and maintain the privacy of their customers’ information.
- Enhanced Productivity: A robust endpoint protection solution not only safeguards against threats but also enhances productivity. By minimizing system downtime caused by malware infections or security breaches, it allows employees to focus on their tasks without interruptions. Additionally, features such as web filtering can prevent access to malicious websites, reducing the risk of accidental downloads and improving overall browsing efficiency.
In conclusion, endpoint protection plays a vital role in safeguarding our digital lives. By deploying a comprehensive security solution that combines multiple layers of defence, real-time threat intelligence, centralized management, data loss prevention measures, and productivity enhancements, we can fortify our devices against the ever-evolving cyber threats that surround us.
Remember, investing in robust endpoint protection is an investment in peace of mind – knowing that your digital frontline is well-protected against potential intruders. Stay vigilant and stay safe in the digital realm!
7 Advantages of Endpoint Protection: Bolstered Security, Enhanced Compliance, Heightened Visibility, Automated Updates, Robust Data Encryption, Cost-Efficiency, and Tranquility
- Increased Security
- Improved Compliance
- Enhanced Visibility
- Automated Updates
- Data Encryption
- Cost Savings
- Peace of Mind
6 Drawbacks of Endpoint Protection: A Comprehensive Analysis of Cons in English (UK)
- High cost – Endpoint protection solutions can be expensive and require a significant financial investment.
- Complex setup – Depending on the type of solution, setting up endpoint protection can be complex and time-consuming.
- Resource intensive – Endpoint protection solutions often require a lot of system resources, which can slow down computers or networks.
- False positives – Some endpoint protection solutions may generate false alarms, which can be disruptive and lead to unnecessary investigations.
- Limited coverage – Not all types of threats are covered by endpoint protection solutions, so other security measures must also be taken to protect against a full range of threats.
- Security gaps– Even with an endpoint protection solution in place, there may still be areas that are vulnerable to attack due to misconfigurations or other weaknesses in the system architecture or configuration settings
Increased Security
Increased Security: Strengthening Your Digital Defences with Endpoint Protection
In the ever-expanding digital landscape, security breaches and malicious attacks have become an unfortunate reality. To counter these threats, businesses and individuals alike are turning to endpoint protection as a crucial security measure. By providing an additional layer of security, endpoint protection helps safeguard systems against malicious attacks and data breaches.
Endpoint protection acts as a formidable shield, fortifying your devices and networks against a wide range of cyber threats. It combines various security measures such as antivirus scanning, firewall protection, behavioural analysis, and intrusion detection systems to create a robust defence system.
One of the primary advantages of endpoint protection is its ability to detect and prevent malicious attacks in real-time. By continuously monitoring endpoints for suspicious activities or known threat signatures, it can swiftly identify potential threats before they can cause harm. This proactive approach significantly reduces the risk of malware infections or unauthorized access to sensitive data.
Moreover, endpoint protection solutions often come equipped with advanced threat intelligence capabilities. These solutions leverage global threat feeds and employ machine learning algorithms to analyze patterns and behaviours across multiple endpoints. This enables them to identify emerging threats that may not yet be recognized by traditional security measures. By staying one step ahead of cybercriminals, endpoint protection enhances the overall security posture of your system.
Another key benefit is that endpoint protection can help mitigate the impact of data breaches. Whether it’s customer information or proprietary business data, protecting sensitive data is paramount in today’s regulatory environment. Endpoint protection solutions implement encryption protocols, access controls, and data loss prevention measures to ensure that confidential information remains secure. By reducing the risk of data breaches, businesses can maintain their reputation while complying with privacy regulations.
By implementing endpoint protection, you not only enhance your system’s security but also gain peace of mind knowing that you have taken proactive steps to protect your valuable assets from cyber threats. With an additional layer of defence in place, you can focus on your work or personal activities without constantly worrying about potential attacks.
In conclusion, endpoint protection offers increased security by providing an additional layer of defence against malicious attacks and data breaches. Its real-time threat detection, advanced threat intelligence, and data protection measures help safeguard systems and sensitive information. By investing in endpoint protection, you are taking a proactive stance towards protecting your digital assets and ensuring a safer online experience.
Improved Compliance
Improved Compliance: Ensuring Business Security and Regulatory Adherence with Endpoint Protection
In an era where data breaches and cyber threats are on the rise, businesses face increasing pressure to comply with stringent industry regulations. This is where endpoint protection steps in, offering a valuable pro: improved compliance.
Endpoint protection solutions provide businesses with the necessary tools to monitor and enforce security policies, helping them meet regulatory requirements. Let’s explore how endpoint protection contributes to enhanced compliance:
- Policy Monitoring and Enforcement: Endpoint protection solutions offer robust features that enable businesses to establish and enforce security policies across all connected devices. These policies can include measures such as data encryption, access controls, software patching, and network restrictions. By monitoring endpoints for policy violations and enforcing compliance measures, businesses can mitigate risks associated with non-compliance.
- Data Protection: Compliance regulations often emphasize the importance of safeguarding sensitive data. Endpoint protection solutions assist in achieving this by implementing data loss prevention (DLP) measures. These measures include encryption, access controls, and monitoring of data transfers both within the network and outside it. By ensuring that confidential information remains secure, businesses can meet regulatory requirements related to data protection.
- Audit Trail Creation: Many industry regulations necessitate maintaining detailed records of security events and activities for auditing purposes. Endpoint protection solutions often include logging capabilities that capture information such as user activities, system changes, and security incidents. These audit trails serve as crucial evidence during compliance audits or investigations.
- Reporting Capabilities: To demonstrate adherence to industry regulations, businesses need comprehensive reports on their security posture and policy enforcement efforts. Endpoint protection solutions typically offer reporting functionalities that provide insights into security incidents, policy violations, malware detection rates, software vulnerabilities, and more. These reports help businesses identify areas for improvement while showcasing their commitment to compliance.
- Notification Systems: Compliance regulations often require prompt notification of security incidents or breaches to relevant authorities or affected individuals. Endpoint protection solutions can integrate with incident response systems, enabling businesses to quickly detect and respond to security events. This swift action helps meet regulatory obligations and minimizes the impact of potential breaches.
By leveraging endpoint protection solutions, businesses can streamline their compliance efforts and ensure adherence to industry regulations. The ability to monitor and enforce security policies, protect sensitive data, create audit trails, generate comprehensive reports, and facilitate timely notifications contributes significantly to achieving compliance objectives.
Moreover, compliance goes beyond meeting regulatory obligations; it also builds trust among customers, partners, and stakeholders. Demonstrating a commitment to robust security practices enhances a business’s reputation and instills confidence in its ability to protect sensitive information.
In conclusion, endpoint protection not only protects businesses from cyber threats but also plays a crucial role in helping them achieve compliance with industry regulations. By leveraging the tools provided by endpoint protection solutions, businesses can establish a strong security foundation while meeting the ever-evolving requirements of the digital landscape.
Enhanced Visibility
Enhanced Visibility: Unveiling the Power of Endpoint Protection
In the realm of cybersecurity, knowledge is power. The ability to gain deep insights into user activity, devices, applications, and networks can make all the difference in identifying and mitigating potential threats. This is where endpoint protection truly shines with its enhanced visibility capabilities.
Endpoint protection solutions provide a comprehensive view of the digital landscape, allowing organizations to monitor and analyze various aspects of their endpoints. By having this level of visibility, businesses can quickly identify any suspicious or malicious activities and respond promptly to mitigate risks.
One key advantage of enhanced visibility is the ability to detect abnormal user behavior. Endpoint protection solutions can track user actions and establish baselines for normal behavior. When deviations occur, such as unauthorized access attempts or unusual file transfers, these solutions raise alerts, enabling security teams to investigate potential threats before they escalate.
Moreover, endpoint protection offers insights into device health and compliance. It provides real-time information on device status, including software versions, operating system updates, and patch levels. This visibility allows organizations to ensure that all devices are up-to-date with the latest security patches and configurations, reducing vulnerabilities that could be exploited by attackers.
Visibility into application usage is another crucial aspect provided by endpoint protection solutions. By monitoring application activities on endpoints, organizations can identify potentially risky applications or those that violate security policies. This insight enables proactive measures like blocking or restricting certain applications to prevent potential breaches or data leaks.
Furthermore, endpoint protection enhances network visibility by monitoring network traffic from endpoints. It allows security teams to detect any suspicious network connections or communications that may indicate a compromise or an attempt to exfiltrate data. With this information at hand, organizations can take immediate action to isolate affected endpoints or block malicious traffic.
The power of enhanced visibility offered by endpoint protection cannot be overstated. It empowers organizations with valuable information about their digital environment, enabling them to swiftly respond to potential threats and take proactive measures to strengthen their security posture.
By leveraging the insights gained from endpoint protection solutions, businesses can stay one step ahead of cybercriminals and protect their sensitive data and systems effectively. Enhanced visibility acts as a beacon, illuminating potential risks and allowing organizations to navigate the ever-evolving landscape of cybersecurity with confidence.
In conclusion, endpoint protection’s ability to provide enhanced visibility into user activity, devices, applications, and networks is a game-changer in the fight against cyber threats. It equips organizations with the knowledge they need to identify potential risks promptly and respond accordingly, ultimately bolstering their overall security defenses.
Automated Updates
Automated Updates: Keeping Your Endpoint Protection Strong
In the fast-paced world of cybersecurity, staying up-to-date with the latest security measures is crucial to effectively combat evolving threats. This is where the pro of automated updates in endpoint protection comes into play.
Regular updates are essential for maintaining the strength and effectiveness of your endpoint protection solution. Automated updates take this process a step further by ensuring that your security software is always equipped with the latest security patches and features without requiring manual intervention.
The importance of automated updates cannot be overstated. Here’s why:
- Enhanced Security: Cybercriminals are constantly developing new techniques to exploit vulnerabilities in software and gain unauthorized access to devices and data. Automated updates help keep your endpoint protection solution fortified against these threats by delivering timely security patches. By promptly addressing vulnerabilities, these updates significantly reduce the risk of attacks and data loss.
- Time-Saving Convenience: Manually updating each device’s security software can be a time-consuming task, especially in organizations with numerous endpoints. With automated updates, this process becomes effortless as the software automatically checks for new updates and installs them seamlessly in the background. This frees up valuable time for IT teams to focus on other critical tasks while ensuring that all devices remain protected.
- Improved Performance: In addition to patching security vulnerabilities, automated updates often include performance enhancements and bug fixes. These improvements optimize the efficiency of your endpoint protection solution, resulting in smoother operation and reduced system resource consumption. As a result, you can enjoy seamless protection without compromising device performance or user experience.
- Compliance and Regulations: Many industries have strict compliance requirements regarding data privacy and security standards. Regularly updating your endpoint protection solution helps ensure that you meet these regulatory obligations by implementing the latest security measures recommended by industry authorities. Compliance not only protects sensitive information but also helps build trust among customers and stakeholders.
- Future-Proofing: The threat landscape is ever-evolving, with new attack vectors and malware strains emerging regularly. Automated updates ensure that your endpoint protection solution is equipped to handle these emerging threats. By keeping your software up-to-date, you stay ahead of cybercriminals and maintain a strong defence against the latest attack techniques.
In conclusion, automated updates are a significant advantage of endpoint protection solutions. By streamlining the process of delivering security patches and feature enhancements, they enhance the overall security posture of your devices while saving time and effort. With automated updates, you can rest assured that your endpoint protection is continuously strengthened to combat the ever-changing cybersecurity landscape.
Data Encryption
Endpoint Protection: Safeguarding Sensitive Data through Encryption
In an era where data breaches and cyber threats are prevalent, protecting sensitive information has become a top priority for individuals and organizations alike. One significant advantage of endpoint protection is its ability to encrypt data stored on endpoints, providing an additional layer of security that ensures confidentiality even in the event of device theft or compromise.
Data encryption is the process of converting plain text into ciphertext, making it unreadable without the appropriate decryption key. Endpoint protection solutions offer robust encryption algorithms that safeguard data at rest on individual devices. This means that even if a laptop, smartphone, or tablet falls into the wrong hands, the encrypted data remains inaccessible and useless to unauthorized individuals.
The importance of data encryption cannot be overstated. It prevents unauthorized access to sensitive information such as personal details, financial records, intellectual property, and trade secrets. By encrypting data at the endpoint level, endpoint protection effectively mitigates the risk of potential data breaches and minimizes the potential damage caused by unauthorized access.
Moreover, endpoint protection solutions often provide centralized management consoles that enable administrators to enforce encryption policies across all connected devices. This ensures consistent application of encryption measures throughout an organization’s network infrastructure. Administrators can define specific encryption protocols based on industry standards or compliance requirements, further enhancing security and maintaining regulatory compliance.
Data encryption also plays a crucial role in protecting information during data transfer between endpoints. Whether it’s sending files via email or sharing documents through cloud storage services, endpoint protection ensures that sensitive information remains encrypted while in transit. This safeguards against interception by malicious actors attempting to eavesdrop on communication channels.
By implementing robust data encryption as part of endpoint protection strategies, organizations can instill confidence in their customers and stakeholders regarding their commitment to protecting sensitive information. Encryption not only helps prevent financial losses resulting from data breaches but also safeguards an organization’s reputation and maintains trust with clients.
In conclusion, the ability of endpoint protection solutions to encrypt data stored on endpoints is a significant advantage in the fight against cyber threats. By rendering sensitive information unreadable to unauthorized individuals, encryption provides an additional layer of security and ensures data confidentiality. With the ever-increasing value of data and the growing sophistication of cyber attacks, incorporating endpoint protection with strong data encryption is a vital step towards comprehensive cybersecurity.
Cost Savings
Cost Savings: The Financial Advantage of Endpoint Protection
In an era where businesses strive to optimize their operations and maximize cost efficiency, endpoint protection emerges as a valuable asset. One notable advantage is the potential for significant cost savings. By investing in robust endpoint protection solutions, businesses can reduce the need for manual patching and other time-consuming tasks associated with maintaining security on individual devices or networks of computers.
Traditionally, ensuring the security of each device within a network required substantial manual effort. IT personnel would spend countless hours applying patches, updates, and security configurations across numerous devices. This process not only consumed valuable time but also increased the risk of human error, potentially leaving vulnerabilities unaddressed.
Endpoint protection streamlines this process by automating many security-related tasks. With centralized management consoles and automated updates, patches can be deployed seamlessly across all connected devices with minimal human intervention. This significantly reduces the time and resources required to maintain a secure network.
By minimizing the need for manual intervention, businesses can allocate their IT resources more effectively. IT teams can focus on strategic initiatives rather than spending excessive time on routine maintenance tasks. This shift in priorities enhances productivity and allows businesses to make the most of their skilled workforce.
Furthermore, endpoint protection helps prevent costly security breaches that could result from unpatched vulnerabilities. A single successful cyber-attack can have severe financial implications for a business, including loss of sensitive data, damage to reputation, legal consequences, and potential downtime. By proactively addressing vulnerabilities through automated patching and continuous monitoring, endpoint protection significantly reduces the risk of such incidents occurring.
In addition to direct financial savings from reduced manual effort and mitigated risks, endpoint protection indirectly contributes to cost savings by minimizing system downtime. Malware infections or security breaches can lead to significant disruptions in business operations, resulting in lost productivity and revenue. By preventing or swiftly resolving these issues through proactive security measures, businesses can maintain uninterrupted workflows and avoid costly downtime.
Investing in endpoint protection is not just about protecting your business; it is also about optimizing your financial resources. By reducing the need for manual patching and other security-related tasks, businesses can achieve cost savings, improve productivity, and minimize the financial risks associated with cyber threats. Endpoint protection proves to be a smart investment that pays dividends in both security and financial terms.
Peace of Mind
Peace of Mind: The Power of Endpoint Protection
In today’s digital landscape, businesses are constantly exposed to a multitude of cyber threats. From sophisticated malware to targeted phishing attacks, the risks can be daunting. This is where endpoint protection steps in, offering a powerful solution that provides peace of mind to businesses.
Endpoint protection serves as a robust shield, safeguarding valuable assets and sensitive data from the ever-evolving tactics employed by malicious actors online. By implementing a comprehensive security solution, businesses can rest easy knowing that they are taking proactive measures to protect their digital infrastructure.
One of the key benefits of endpoint protection is the peace of mind it brings. Knowing that your business is secure from cyber threats instills confidence and allows you to focus on what truly matters – growing your business and serving your customers.
Endpoint protection offers several features that contribute to this sense of security:
- Advanced Threat Detection: Endpoint protection solutions employ advanced algorithms and machine learning techniques to detect and prevent both known and unknown threats. With real-time monitoring and analysis, these solutions can identify suspicious activities and promptly respond to potential breaches before they cause significant damage.
- Proactive Defence: Endpoint protection takes a proactive approach by continuously updating its threat intelligence database. This ensures that businesses have access to the latest information about emerging threats, enabling them to stay one step ahead of cybercriminals. By actively monitoring for vulnerabilities and deploying timely patches or updates, businesses can mitigate risks effectively.
- Data Protection: Endpoint protection not only focuses on preventing external attacks but also safeguards against internal threats. It helps protect sensitive data by implementing encryption measures, access controls, and data loss prevention techniques. This ensures that even if a device falls into the wrong hands or an employee inadvertently compromises security, critical information remains protected.
- Centralized Management: Many endpoint protection solutions offer centralized management consoles that allow administrators to monitor and manage security policies across all endpoints from a single interface. This centralized approach provides visibility into the overall security posture of the network, making it easier to identify potential vulnerabilities and take proactive measures to address them.
By investing in endpoint protection, businesses demonstrate their commitment to securing their valuable assets and data. This not only protects their reputation but also builds trust among customers and partners, who can be confident that their information is handled with care.
In conclusion, endpoint protection offers businesses peace of mind by providing comprehensive security against cyber threats. By implementing advanced threat detection, proactive defence mechanisms, robust data protection measures, and centralized management, businesses can rest assured that they are doing everything possible to safeguard their digital infrastructure.
Remember, peace of mind is invaluable in today’s digital world. Protecting your business from cyber threats not only preserves your assets but also allows you to focus on what truly matters – driving success and growth while maintaining the trust of your stakeholders.
High cost – Endpoint protection solutions can be expensive and require a significant financial investment.
High Cost: A Consideration in Endpoint Protection
When it comes to endpoint protection, one aspect that organizations and individuals need to carefully consider is the potential high cost associated with implementing these solutions. While endpoint protection offers a multitude of benefits, it’s important to weigh the financial implications before making a decision.
Endpoint protection solutions often come with a price tag that includes licensing fees, subscription costs, and ongoing maintenance expenses. For small businesses or individuals on a tight budget, these expenses can pose a significant financial burden. The need for multiple licenses to cover all endpoints within an organization can further escalate costs.
Additionally, as cyber threats continue to evolve and become more sophisticated, endpoint protection providers frequently release updates and patches to ensure optimal security. These updates may require additional fees or upgraded subscriptions, further adding to the overall cost of maintaining effective endpoint protection.
However, while the initial investment may be substantial, it is important to consider the potential consequences of not having adequate protection in place. The cost of recovering from a cyberattack or data breach can far outweigh the expense of implementing robust endpoint protection. The loss of sensitive data, damage to reputation, legal repercussions, and disruption of business operations can have long-lasting financial implications that are often far more severe than the initial investment in security measures.
To mitigate the impact of high costs associated with endpoint protection solutions, it is advisable to conduct thorough research and consider various options available in the market. Comparing prices and features offered by different vendors can help identify cost-effective solutions without compromising on security.
Furthermore, organizations can explore managed service providers (MSPs) that offer endpoint protection as part of their services. This approach allows businesses to outsource their security needs to experts who can provide tailored solutions at a more affordable rate compared to maintaining an in-house IT team solely dedicated to managing endpoint security.
Ultimately, while high costs may be seen as a con of implementing endpoint protection solutions, it is crucial not to overlook the potential risks and financial consequences of neglecting proper security measures. By carefully evaluating the available options, organizations and individuals can strike a balance between cost-effectiveness and ensuring robust protection for their digital assets.
Complex setup – Depending on the type of solution, setting up endpoint protection can be complex and time-consuming.
Endpoint Protection: The Challenge of Complex Setup
While endpoint protection is undoubtedly a crucial aspect of modern cybersecurity, it is essential to acknowledge that it comes with its fair share of challenges. One notable drawback is the complex and time-consuming setup process that can be associated with certain types of solutions.
Implementing endpoint protection often requires careful planning and configuration to ensure seamless integration with existing IT infrastructure. This complexity arises from various factors, including the diversity of devices, operating systems, and software applications within an organization.
Different endpoints may require specific configurations and settings to maximize their security effectiveness. For instance, laptops may need different security measures compared to smartphones or servers. Additionally, compatibility issues can arise when integrating endpoint protection solutions with other security tools or network components.
Moreover, some advanced endpoint protection solutions offer a wide range of features and customization options. While this flexibility is advantageous in tailoring the solution to specific needs, it can also lead to a more intricate setup process. Configuring multiple layers of defence mechanisms, defining policies, and fine-tuning settings can be time-consuming for IT administrators.
The complexity of setting up endpoint protection can also be influenced by factors such as the size of an organization and the level of technical expertise available. Smaller businesses with limited IT resources may find it more challenging to navigate through the setup process compared to larger enterprises with dedicated IT teams.
However, it’s important to note that not all endpoint protection solutions are equally complex in terms of setup. Many providers recognize this challenge and strive to simplify the onboarding experience for their customers by offering intuitive user interfaces, step-by-step guides, and automated deployment options.
To mitigate the potential difficulties associated with complex setup processes, organizations should consider engaging with reputable vendors who provide comprehensive support services. These services can include professional assistance during deployment, training sessions for IT staff members, and ongoing technical support throughout the lifecycle of the solution.
While acknowledging the challenge presented by complex setup processes in some cases, it is crucial to remember that the long-term benefits of endpoint protection generally outweigh the initial setup complexities. The enhanced security, protection against cyber threats, and peace of mind that come with a well-implemented solution make the investment worthwhile.
In conclusion, while it is true that setting up endpoint protection can be complex and time-consuming depending on the type of solution chosen, organizations can overcome these challenges with proper planning, vendor support, and training. By carefully considering their specific needs and partnering with reliable providers, businesses can ensure a smooth implementation process while reaping the significant benefits of robust endpoint protection.
Resource intensive – Endpoint protection solutions often require a lot of system resources, which can slow down computers or networks.
Resource Intensive: The Trade-Off of Endpoint Protection
While endpoint protection solutions offer a wide array of benefits, it is important to acknowledge that they come with their own set of challenges. One common drawback is that these security measures can be resource-intensive, potentially impacting the performance of computers or networks.
Endpoint protection solutions typically run in the background, constantly monitoring and scanning for potential threats. This continuous process requires a significant amount of system resources such as CPU power, memory, and network bandwidth. As a result, computers or networks may experience slower response times and reduced overall performance.
The resource-intensive nature of endpoint protection can be particularly noticeable on older or less powerful devices. These systems may struggle to keep up with the demands placed on them by the security software, leading to sluggishness and delays in executing tasks.
However, it is essential to consider this con in perspective. While there may be some impact on system performance, the benefits provided by endpoint protection often outweigh this trade-off. The potential risks associated with cyber threats far outweigh the inconvenience caused by slightly slower systems.
Fortunately, many endpoint protection solutions have made significant advancements in optimizing their resource usage. Developers are continuously working towards improving efficiency without compromising security standards. It is advisable to choose reputable and well-established vendors who prioritize finding a balance between effective protection and minimal impact on system resources.
To mitigate the impact of resource-intensive endpoint protection, there are a few steps that users can take:
- Regularly update software: Keeping your endpoint protection software up to date ensures that you benefit from the latest optimizations and improvements designed to minimize resource usage.
- Configure scans and updates: Adjusting scan schedules and update settings can help distribute resource usage more evenly throughout the day, avoiding peak usage periods when system activity is high.
- Upgrade hardware: If you consistently face performance issues due to endpoint protection software, upgrading your hardware – such as adding more RAM or opting for faster processors – can help alleviate the strain on system resources.
In conclusion, while it is true that endpoint protection solutions can be resource-intensive and potentially impact system performance, the benefits they provide in terms of safeguarding against cyber threats are crucial. By carefully selecting reputable vendors and implementing best practices, users can strike a balance between security and system performance, ensuring a safer digital environment without compromising efficiency.
False positives – Some endpoint protection solutions may generate false alarms, which can be disruptive and lead to unnecessary investigations.
Navigating the Conundrum of False Positives in Endpoint Protection
While endpoint protection solutions offer a crucial line of defence against cyber threats, it is important to acknowledge that no security measure is perfect. One common drawback that users may encounter is the occurrence of false positives – instances where the protection software mistakenly identifies legitimate files or activities as malicious. Although false positives are an unintended consequence, they can be disruptive and lead to unnecessary investigations.
False positives occur when the endpoint protection software misinterprets certain behaviours or files as potential threats. This can happen due to various reasons, such as outdated threat intelligence databases, overly sensitive scanning algorithms, or even complex system configurations that trigger false alarms. Although these incidents are unintentional, they can cause frustration and consume valuable time and resources.
One significant impact of false positives is the disruption they can cause in daily operations. Legitimate files or applications flagged as malicious may be blocked or quarantined, rendering them temporarily inaccessible to users. This interruption can lead to delays in critical tasks and productivity loss for individuals or organizations relying on those files or applications.
Moreover, false positives can also erode trust in the endpoint protection solution itself. Frequent false alarms may lead users to question the reliability and accuracy of the software, potentially prompting them to disable or bypass certain security features altogether. This unintended consequence could leave systems vulnerable to genuine threats and compromise overall security.
To mitigate the impact of false positives, it is essential for endpoint protection providers to continually improve their detection algorithms and update their threat intelligence databases promptly. By refining their software’s ability to distinguish between genuine threats and harmless activities, providers can minimize instances of false alarms.
Users also play a role in managing false positives effectively. Understanding how their endpoint protection solution works and its sensitivity levels allows them to calibrate settings accordingly. Regularly updating software versions and maintaining open communication with the provider’s support team can help address any issues promptly.
In conclusion, while false positives present a conundrum within endpoint protection, it is crucial to recognize that they are unintended consequences rather than deliberate flaws. By acknowledging the possibility of false alarms and adopting proactive measures to manage them effectively, users can strike a balance between maintaining robust security and minimizing disruptions caused by false positives.
Limited coverage – Not all types of threats are covered by endpoint protection solutions, so other security measures must also be taken to protect against a full range of threats.
Endpoint Protection: Addressing the Limitations
Endpoint protection has become an indispensable aspect of modern cybersecurity, providing a strong defence against a wide array of threats. However, it is important to acknowledge that like any security solution, it does have its limitations. One such limitation is the limited coverage it offers.
While endpoint protection solutions excel at detecting and mitigating many common threats, they may not cover all types of cyber attacks. This means that additional security measures must be implemented to ensure comprehensive protection against the full range of potential threats.
Endpoint protection primarily focuses on securing individual devices, such as laptops, smartphones, and tablets. It employs various techniques like antivirus scanning, behavioural analysis, and firewall protection to safeguard these endpoints from malware infections and other known threats. However, emerging threats like zero-day exploits or sophisticated targeted attacks can sometimes evade detection by traditional endpoint protection solutions.
To address this limitation and ensure holistic security, organizations should adopt a multi-layered approach that combines different security solutions. For instance:
- Network Security: Implementing robust network security measures such as firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS) can help detect and block malicious activities before they reach the endpoints.
- Email Security: Since email remains one of the primary attack vectors for phishing attempts and malware distribution, deploying advanced email security solutions can provide an additional layer of defence by scanning incoming emails for malicious content or suspicious links.
- Web Security: Web filtering solutions can prevent users from accessing malicious websites known for hosting malware or engaging in phishing activities. By blocking access to such sites at the network level, organizations can reduce the risk of users unintentionally downloading harmful content.
- User Education: No security solution can fully protect against human error or social engineering attacks. Educating employees about safe browsing practices, recognizing phishing attempts, and maintaining strong passwords is crucial in fortifying the overall cybersecurity posture.
By integrating these complementary security measures alongside endpoint protection, organizations can mitigate the limitations of limited coverage. This multi-layered approach ensures a more comprehensive defence against a broader spectrum of threats, including both known and emerging ones.
In conclusion, while endpoint protection is a powerful tool in the fight against cyber threats, it is essential to acknowledge its limitations. By adopting a multi-layered security strategy that combines different solutions and fostering a culture of cybersecurity awareness, organizations can create a robust defence that addresses the full range of potential threats. Remember, cybersecurity is an ongoing process that requires continuous evaluation and adaptation to stay ahead of evolving threats.
Security gaps– Even with an endpoint protection solution in place, there may still be areas that are vulnerable to attack due to misconfigurations or other weaknesses in the system architecture or configuration settings
Exploring the Con of Endpoint Protection: Security Gaps
Endpoint protection solutions are undoubtedly crucial in fortifying our digital devices against a multitude of cyber threats. However, it is essential to acknowledge that even with such solutions in place, there can be potential security gaps that attackers may exploit. These gaps arise due to misconfigurations or weaknesses in the system architecture or configuration settings.
One of the primary reasons for these security gaps is human error. Despite the advanced capabilities of endpoint protection solutions, they rely on proper configuration and ongoing maintenance to remain effective. If administrators overlook critical settings or fail to update the solution regularly, vulnerabilities can emerge, leaving endpoints exposed to potential attacks.
Furthermore, misconfigurations within network infrastructure can create security gaps. For instance, if firewalls and intrusion detection systems are not appropriately configured or lack regular updates, they may fail to detect and prevent sophisticated attacks. Attackers can exploit these weak points to gain unauthorized access to sensitive data or compromise the integrity of the system.
Another factor contributing to security gaps is the complexity of modern IT environments. Organizations often have a diverse range of devices, operating systems, and applications interconnected within their networks. Managing and securing this complex ecosystem can be challenging, leading to unintentional oversights or inconsistencies that leave certain endpoints vulnerable.
Moreover, emerging technologies like cloud computing and remote work arrangements introduce additional complexities. Organizations must ensure that their endpoint protection solutions are seamlessly integrated into these environments without compromising security. Failure to do so can result in security gaps that adversaries may exploit.
To address this con effectively, organizations must prioritize continuous monitoring and proactive management of their endpoint protection solutions. Regular audits should be conducted to identify any misconfigurations or weaknesses in the system architecture promptly. Additionally, ongoing training and awareness programs for administrators and end-users can help mitigate human errors that could lead to security gaps.
Collaboration with experienced cybersecurity professionals is also crucial in addressing these vulnerabilities effectively. They can provide guidance on best practices, assist in conducting security assessments, and offer recommendations on how to strengthen the system architecture and configuration settings.
While security gaps in endpoint protection solutions are a genuine concern, they can be mitigated through a combination of diligent management practices, regular audits, and collaboration with experts. By acknowledging these potential weaknesses and taking proactive steps to address them, organizations can enhance their overall security posture and minimize the risk of successful cyber attacks.