Enhancing Cybersecurity with ThreatConnect and Splunk Integration
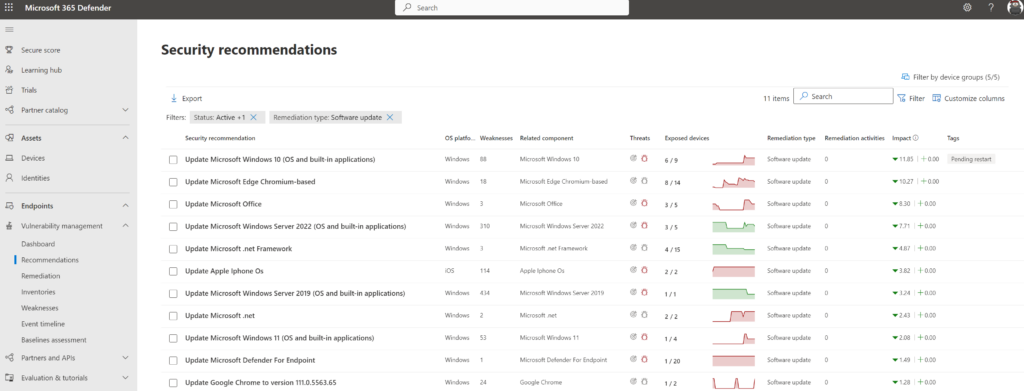
Exploring ThreatConnect and Splunk: Strengthening Cybersecurity Exploring ThreatConnect and Splunk: Strengthening Cybersecurity In the realm…
0 Comments