Data Network Security: Safeguarding Your Digital Assets
In today’s interconnected world, data network security plays a critical role in protecting sensitive information and ensuring the integrity of digital communications. With the increasing volume and complexity of cyber threats, organisations and individuals must prioritise robust security measures to safeguard their data.
Effective data network security involves implementing a multi-layered approach to prevent unauthorised access, data breaches, and other malicious activities. This includes:
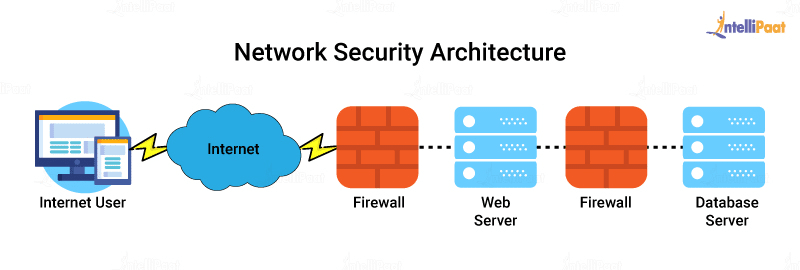
- Firewalls: Firewalls act as a barrier between your internal network and external threats, monitoring and controlling incoming and outgoing network traffic based on predetermined security rules.
- Encryption: Encrypting data ensures that even if it is intercepted, it remains unreadable without the appropriate decryption key, adding an extra layer of protection.
- Access Control: Implementing strict access controls limits who can view or modify sensitive data, reducing the risk of insider threats and unauthorised access.
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): IDS and IPS monitor network traffic for suspicious activity or known attack patterns, alerting administrators or taking automated action to block potential threats.
Regularly updating software, conducting security audits, training employees on best practices, and establishing incident response plans are also essential components of a comprehensive data network security strategy. By staying proactive and vigilant, organisations can mitigate risks and protect their digital assets from evolving cyber threats.
Investing in data network security is not just about compliance or avoiding financial losses; it is about safeguarding trust with customers, partners, and stakeholders. A breach in security can have far-reaching consequences beyond financial implications, including reputational damage and legal repercussions.
In conclusion, data network security is a fundamental aspect of modern business operations. By adopting a holistic approach to cybersecurity that combines technology, policies, and employee awareness, organisations can create a secure environment for their digital assets to thrive.
Essential Data and Network Security: Understanding Types, Elements, and Key Differences
- What are the three types of data security?
- What are the 3 types of data security?
- What are the four 4 elements of data security?
- What are the four types of network security?
- What’s the difference between IDS and IPS?
What are the three types of data security?
Data network security encompasses various aspects of safeguarding sensitive information, and understanding the three primary types of data security is crucial in establishing a robust defence strategy. The three main types of data security include physical security, technical security, and administrative security. Physical security involves protecting hardware and physical assets that store data, such as servers and storage devices. Technical security focuses on implementing technologies like encryption, firewalls, and intrusion detection systems to secure data during transmission and storage. Administrative security involves establishing policies, procedures, and user access controls to manage data securely within an organisation. By addressing these three key areas of data security comprehensively, businesses can fortify their defences against cyber threats effectively.
What are the 3 types of data security?
Data security encompasses various measures to protect sensitive information from unauthorised access, breaches, and manipulation. The three main types of data security are physical security, technical security, and administrative security. Physical security involves safeguarding hardware and storage devices that store data, such as servers and laptops, through measures like access controls and surveillance. Technical security focuses on using encryption, firewalls, and intrusion detection systems to secure data during transmission and storage. Administrative security involves establishing policies, procedures, and user access controls to manage data securely within an organisation. By implementing a combination of these three types of data security measures, organisations can enhance their overall cybersecurity posture and protect valuable information from potential threats.
What are the four 4 elements of data security?
Data security encompasses four key elements that are essential in safeguarding sensitive information within a network. These elements include encryption, access control, data integrity, and authentication. Encryption ensures that data is encoded to prevent unauthorised access, while access control limits who can view or modify the data. Data integrity verifies that data remains unchanged and uncorrupted during storage or transmission, and authentication validates the identity of users accessing the data. By incorporating these four elements into a comprehensive data security strategy, organisations can enhance their resilience against cyber threats and protect valuable digital assets effectively.
What are the four types of network security?
When it comes to data network security, understanding the four types of network security is crucial for establishing a robust defence against cyber threats. The four main types of network security include physical security, network security, application security, and endpoint security. Physical security involves protecting the physical infrastructure of a network, such as servers and data centres. Network security focuses on securing the communication channels within a network to prevent unauthorised access or data breaches. Application security aims to protect software applications from vulnerabilities that could be exploited by attackers. Endpoint security involves securing individual devices connected to a network, such as laptops and smartphones, to prevent malware infections and other cyber attacks. By addressing each of these types of network security comprehensively, organisations can enhance their overall cybersecurity posture and safeguard their valuable data assets.
What’s the difference between IDS and IPS?
In the realm of data network security, a common query often arises regarding the distinction between Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS). While both serve as vital components in safeguarding networks, their primary variances lie in their functionalities. An IDS is designed to monitor network traffic, identifying potential threats and anomalies by analysing patterns and signatures. Conversely, an IPS not only detects suspicious activities but also takes proactive measures to block or mitigate these threats in real-time, thereby preventing potential security breaches before they occur. Understanding the nuanced disparity between IDS and IPS is crucial in implementing a comprehensive security strategy that effectively combats cyber threats and fortifies network defences.