The Benefits of Using Check Point Mobile VPN
Check Point Mobile VPN is a powerful tool that provides secure remote access to corporate networks for mobile users. With the increasing number of employees working remotely or on the go, having a reliable VPN solution is essential to ensure data security and privacy.
Secure Remote Access
One of the key advantages of Check Point Mobile VPN is its ability to establish a secure connection between mobile devices and corporate networks. This encrypted connection prevents unauthorized access and protects sensitive data from potential threats.
User-Friendly Interface
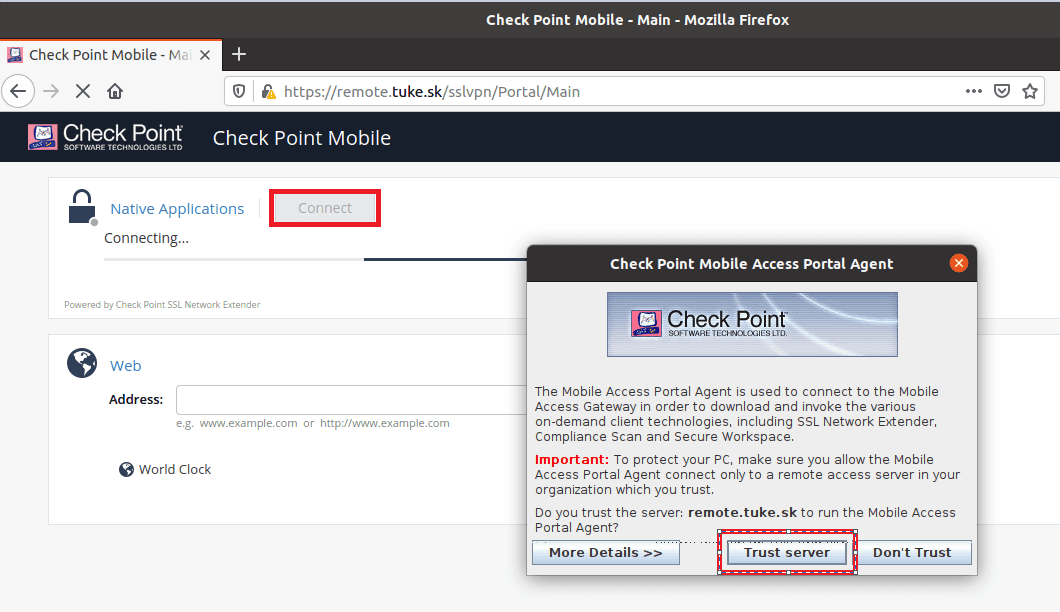
Check Point Mobile VPN offers a user-friendly interface that makes it easy for users to connect to the corporate network with just a few clicks. Whether you are working from home, a coffee shop, or while travelling, you can quickly establish a secure connection without compromising on usability.
Multi-Platform Support
Check Point Mobile VPN supports multiple platforms, including iOS and Android devices, ensuring that users can securely access corporate resources regardless of their device preferences. This flexibility allows organisations to accommodate diverse mobile device ecosystems within their workforce.
Enhanced Security Features
In addition to encrypting data transmissions, Check Point Mobile VPN offers advanced security features such as multi-factor authentication and endpoint compliance checks. These additional layers of security help prevent unauthorised access and ensure that only compliant devices can connect to the corporate network.
24/7 Technical Support
Check Point provides round-the-clock technical support for its Mobile VPN solution, ensuring that users have access to assistance whenever they encounter issues or require guidance. This responsive support system enhances user experience and minimises downtime due to technical challenges.
Conclusion
Check Point Mobile VPN is a reliable solution for organisations looking to provide secure remote access for their mobile workforce. With its robust security features, user-friendly interface, and multi-platform support, Check Point Mobile VPN offers a comprehensive solution for safeguarding sensitive data and maintaining productivity in today’s mobile-centric work environment.
9 Essential Tips for Securing Your Check Point Mobile VPN Connection
- Ensure your Check Point Mobile VPN client is up to date.
- Use strong and unique passwords for your VPN connection.
- Enable two-factor authentication for added security.
- Regularly check for any security patches or updates for the VPN client.
- Avoid connecting to public Wi-Fi networks without using the VPN.
- Disconnect from the VPN when not in use to prevent unauthorized access.
- Configure firewall settings to enhance security while using the VPN.
- Keep logs of your VPN connections for monitoring and troubleshooting purposes.
- Contact support if you encounter any issues with your Check Point Mobile VPN.
Ensure your Check Point Mobile VPN client is up to date.
To maximise the security and performance of your Check Point Mobile VPN, it is crucial to ensure that your VPN client is always up to date. Regularly updating the client software not only ensures that you have access to the latest security patches and features but also helps in addressing any potential vulnerabilities that could be exploited by cyber threats. By keeping your Check Point Mobile VPN client up to date, you can enhance the overall effectiveness of your remote access solution and maintain a secure connection to your corporate network at all times.
Use strong and unique passwords for your VPN connection.
To enhance the security of your Check Point Mobile VPN connection, it is crucial to use strong and unique passwords. By creating complex passwords that are unique to your VPN connection, you can significantly reduce the risk of unauthorised access to your corporate network and sensitive data. Strong passwords should include a mix of letters, numbers, and special characters, making them harder for potential attackers to guess or crack. Remembering to update and change your passwords regularly further strengthens the security of your VPN connection, ensuring that your remote access remains secure and protected against cyber threats.
Enable two-factor authentication for added security.
Enabling two-factor authentication for your Check Point Mobile VPN adds an extra layer of security to protect your remote access to corporate networks. With two-factor authentication in place, even if someone obtains your password, they would still need a second form of verification to gain access. This additional security measure significantly reduces the risk of unauthorised access and enhances the overall protection of sensitive data during remote connections.
Regularly check for any security patches or updates for the VPN client.
It is essential to stay vigilant and proactive when it comes to maintaining the security of your Check Point Mobile VPN client. Regularly checking for security patches and updates is crucial in ensuring that your VPN client is equipped with the latest protections against emerging threats. By promptly installing these patches, you can enhance the overall security posture of your VPN connection and safeguard your data from potential vulnerabilities. Stay informed and proactive to keep your VPN client secure and resilient against cyber threats.
Avoid connecting to public Wi-Fi networks without using the VPN.
To enhance your security while using Check Point Mobile VPN, it is advisable to avoid connecting to public Wi-Fi networks without activating the VPN. Public Wi-Fi networks are inherently vulnerable to cyber threats, making it easy for malicious actors to intercept data transmitted over these networks. By using the VPN, you encrypt your connection and create a secure tunnel that shields your data from potential eavesdropping or attacks on unsecured public Wi-Fi hotspots. This simple precaution can significantly reduce the risk of data breaches and ensure that your sensitive information remains protected while accessing the internet on-the-go.
Disconnect from the VPN when not in use to prevent unauthorized access.
It is important to remember to disconnect from the Check Point Mobile VPN when not in use to prevent unauthorized access to your corporate network and sensitive data. By actively disconnecting from the VPN when you have finished your work session, you reduce the risk of potential security breaches and ensure that only authorised users can access the network. This simple precautionary measure helps maintain the integrity of your connection and enhances overall security for both you and your organisation.
Configure firewall settings to enhance security while using the VPN.
Configuring firewall settings is a crucial tip to enhance security when using Check Point Mobile VPN. By adjusting firewall rules to restrict incoming and outgoing traffic to only essential services and applications, users can strengthen their network’s defences against potential threats. This proactive measure helps to prevent unauthorised access and ensures that data transmitted through the VPN remains secure. By customising firewall settings in conjunction with using the VPN, users can create an additional layer of protection for their devices and data, ultimately bolstering the overall security posture of their remote connections.
Keep logs of your VPN connections for monitoring and troubleshooting purposes.
Keeping logs of your VPN connections when using Check Point Mobile VPN is a valuable practice for monitoring and troubleshooting purposes. By maintaining detailed records of your connection history, you can track usage patterns, identify potential security incidents, and troubleshoot any connectivity issues that may arise. These logs can provide insights into the performance of your VPN connection, help in detecting unusual activities, and assist in diagnosing and resolving technical issues efficiently. Regularly reviewing these logs can enhance the overall security and reliability of your VPN setup, ensuring a smooth and secure remote access experience for mobile users.
Contact support if you encounter any issues with your Check Point Mobile VPN.
If you encounter any issues with your Check Point Mobile VPN, it is advisable to contact the support team for assistance. By reaching out to the dedicated support professionals, you can receive prompt help and guidance to resolve any technical challenges you may face. Whether it’s troubleshooting connectivity issues, addressing configuration problems, or seeking advice on best practices, the support team is there to ensure that your Check Point Mobile VPN operates smoothly and securely. Don’t hesitate to seek help when needed to maximise the effectiveness of your VPN solution.