Understanding Security Information and Event Management (SIEM) Systems
In today’s digital landscape, where cyber threats are constantly evolving, organisations need robust solutions to protect their sensitive data and infrastructure. One such essential tool in the realm of cybersecurity is the Security Information and Event Management (SIEM) system.
A SIEM system is a comprehensive approach to security management that provides real-time analysis of security alerts generated by network hardware and applications. It collects data from various sources, including logs, events, and traffic data, and correlates this information to identify potential security incidents.
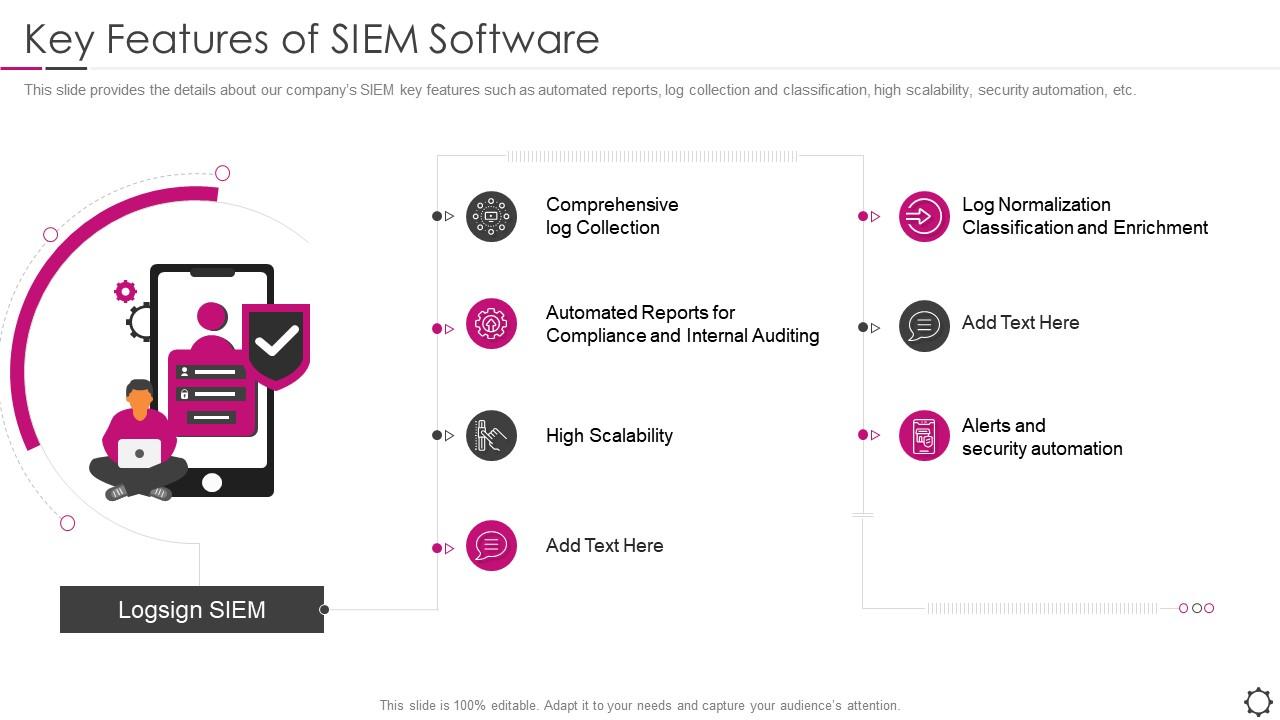
The primary functions of a SIEM system include:
- Log collection: Gathering log data from multiple sources across the network.
- Event correlation: Analysing log data to identify patterns and potential security incidents.
- Alerting: Notifying security personnel of suspicious activities or breaches.
- Incident response: Providing tools for investigating and responding to security incidents.
By centralising security event data and providing real-time monitoring capabilities, SIEM systems enable organisations to detect threats more effectively, respond promptly to incidents, and comply with regulatory requirements.
Furthermore, SIEM systems offer valuable insights into network activity, user behaviour, and system vulnerabilities. This visibility allows security teams to proactively mitigate risks, enhance their incident response strategies, and strengthen overall cybersecurity posture.
Implementing a SIEM system requires careful planning and configuration to ensure optimal performance. Organisations must define their security objectives, establish clear monitoring criteria, integrate relevant data sources, and customise alerting mechanisms based on their specific needs.
In conclusion, Security Information and Event Management (SIEM) systems play a crucial role in modern cybersecurity efforts by providing comprehensive threat detection, incident response capabilities, and actionable insights for enhancing overall security posture. By leveraging the power of SIEM technology, organisations can better protect their assets, mitigate risks effectively, and stay ahead of emerging cyber threats.
Key Advantages of Security Information and Event Management Systems: Enhancing Threat Detection and Operational Efficiency
- Real-time threat detection
- Centralised log management
- Compliance support
- Incident response automation
- User behaviour analysis
- Customisable alerts
- Enhanced visibility
- Scalability
Challenges of Security Information and Event Management Systems: Complexity, Cost, and More
Real-time threat detection
One of the key advantages of Security Information and Event Management (SIEM) systems is their capability for real-time threat detection. By offering continuous monitoring and immediate alerts for potential security incidents, SIEM systems empower organisations to swiftly identify and respond to threats as they emerge. This proactive approach enables security teams to take timely action, mitigating risks and minimising the impact of cyber attacks on their networks and data. The ability to detect threats in real-time is a critical feature that enhances overall cybersecurity resilience and helps organisations stay one step ahead of malicious actors in today’s dynamic threat landscape.
Centralised log management
One key advantage of Security Information and Event Management (SIEM) systems is centralised log management, which allows organisations to streamline the collection and storage of logs from diverse sources in a unified location. This consolidated approach simplifies the analysis process by providing security teams with a single point of access to all relevant log data, enabling them to identify patterns, detect anomalies, and investigate security incidents more efficiently. By centralising log management, organisations can enhance their visibility into network activities, improve incident response times, and strengthen their overall cybersecurity defences.
Compliance support
One significant advantage of Security Information and Event Management (SIEM) systems is their compliance support functionality. By offering detailed audit trails and robust reporting capabilities, SIEM systems enable businesses to meet regulatory requirements effectively. Organisations can easily demonstrate their adherence to industry standards and data protection laws by leveraging the comprehensive monitoring and documentation features of SIEM technology. This proactive approach not only helps in maintaining regulatory compliance but also enhances overall data security and governance practices within the organisation.
Incident response automation
One significant advantage of Security Information and Event Management (SIEM) systems is their incident response automation capability. By incorporating automated response mechanisms, SIEM systems enable organisations to address security breaches swiftly and efficiently. These automated processes can identify and contain threats in real-time, reducing the impact of potential security incidents and minimising the time required for manual intervention. Incident response automation in SIEM systems enhances overall cybersecurity resilience by streamlining response procedures and ensuring a proactive approach to threat mitigation.
User behaviour analysis
User behaviour analysis is a key advantage of Security Information and Event Management (SIEM) systems. By monitoring and analysing user activities, SIEM solutions can detect unusual or suspicious behaviour that deviates from normal patterns. This proactive approach enables organisations to identify potential security threats early on, allowing them to take swift action to mitigate risks and protect their sensitive data and assets. The user behaviour analysis feature of SIEM systems provides valuable insights into insider threats, compromised accounts, and other security incidents that may go unnoticed by traditional security measures.
Customisable alerts
One key advantage of Security Information and Event Management (SIEM) systems is the ability to customise alerts according to the unique security requirements and priorities of organisations. By tailoring alerting rules, businesses can ensure that they receive notifications for specific events or incidents that are most relevant to their security posture. This customisation empowers organisations to focus on critical threats, respond swiftly to potential breaches, and align their security efforts with their strategic objectives effectively. Customisable alerts in SIEM systems enhance the precision and efficiency of incident detection and response, thereby strengthening overall cybersecurity defences.
Enhanced visibility
One key advantage of Security Information and Event Management (SIEM) systems is their ability to offer enhanced visibility into network activity. By providing a comprehensive view of logs, events, and traffic data from various sources, SIEM systems empower organisations to make informed decisions and proactively mitigate risks. This heightened visibility enables security teams to detect anomalies, identify potential threats, and respond swiftly to security incidents, ultimately strengthening the overall cybersecurity posture of the organisation.
Scalability
One significant advantage of Security Information and Event Management (SIEM) systems is their scalability. SIEM solutions are designed to grow alongside an organisation, effectively accommodating the escalating data volumes and evolving security requirements that come with expansion. This scalability ensures that as the business expands, the SIEM system can seamlessly adapt to handle larger datasets and address new security challenges, providing a reliable and flexible security solution for organisations of all sizes.
Complexity
One significant drawback of Security Information and Event Management (SIEM) systems is their inherent complexity. Implementing and managing SIEM systems can be a daunting task, often requiring specialised expertise and dedicated resources. The intricacies involved in configuring data sources, defining correlation rules, and fine-tuning alert mechanisms can pose challenges for organisations without the necessary skills or experience in cybersecurity. The complexity of SIEM systems may lead to delays in deployment, increased operational costs, and potential gaps in security coverage if not managed effectively.
Cost
One notable drawback of Security Information and Event Management (SIEM) systems is the substantial financial burden associated with their implementation. The initial investment required to acquire and set up a SIEM system, coupled with the ongoing maintenance costs, can pose a significant challenge for organisations, especially those with limited budgets. The need for specialised hardware, software licenses, training for personnel, and continuous updates to keep the system effective can contribute to a high total cost of ownership. As a result, the cost factor may deter some organisations from fully realising the benefits of a SIEM system, despite its valuable security capabilities.
False positives
One significant drawback of Security Information and Event Management (SIEM) systems is the issue of false positives. Due to the complexity of correlating data from multiple sources, SIEM systems may produce a considerable volume of false alerts, which can overwhelm security teams and result in alert fatigue. Dealing with a high number of false positives not only consumes valuable time and resources but also increases the risk of genuine security incidents being overlooked or ignored. Effective tuning and fine-tuning of SIEM configurations are essential to reduce false alerts and ensure that security teams can focus on responding to genuine threats efficiently.
Integration challenges
One significant downside of Security Information and Event Management (SIEM) systems is the integration challenges they pose. Integrating diverse data sources into a SIEM system can be a complex and time-consuming process. Organisations often struggle to consolidate logs and events from various sources, such as network devices, applications, and cloud services, into a unified platform. This integration challenge can lead to delays in implementation, increased costs, and potential gaps in monitoring capabilities, ultimately hindering the effectiveness of the SIEM system in detecting and responding to security incidents.
Resource-intensive
One significant drawback of Security Information and Event Management (SIEM) systems is their resource-intensive nature. Monitoring and managing a SIEM system demands dedicated resources and constant attention from skilled personnel. The continuous analysis of security alerts, data correlation, and incident response activities can place a substantial burden on an organisation’s IT team. The need for regular maintenance, updates, and fine-tuning of the system further adds to the resource requirements. As a result, organisations must allocate sufficient manpower and budget to ensure the effective operation of a SIEM system, which can strain limited resources and potentially impact other critical IT initiatives.
Scalability issues
Scalability issues present a significant challenge when it comes to Security Information and Event Management (SIEM) systems. As data volumes and network complexity continue to increase, scaling a SIEM system to effectively handle the growing demand can be a daunting task. The infrastructure required to support large-scale data processing and analysis may strain existing resources, leading to performance bottlenecks and potential gaps in security monitoring. Organisations must carefully consider scalability requirements and implement strategies to ensure that their SIEM system can adapt and expand seamlessly as the environment evolves. Failure to address scalability issues proactively could compromise the system’s effectiveness in detecting and responding to security incidents in a timely manner.