The Importance of Palo Alto Vulnerability Management
In today’s interconnected world, where cyber threats are constantly evolving, robust vulnerability management is crucial to maintaining the security of your network infrastructure. One of the leading solutions in this field is Palo Alto Networks’ vulnerability management platform.
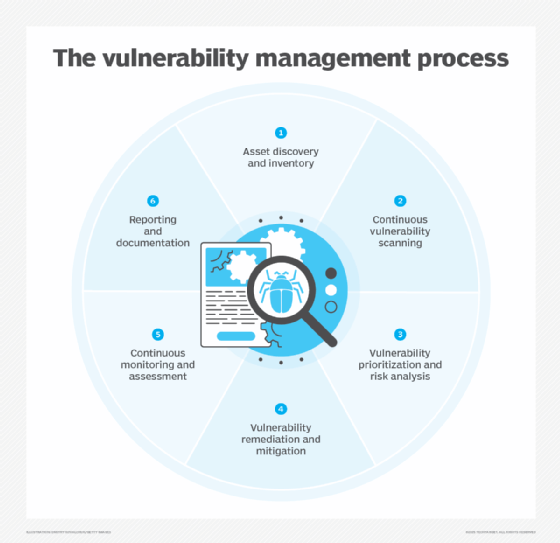
Palo Alto vulnerability management offers a comprehensive approach to identifying, prioritising, and addressing security vulnerabilities within your network. By leveraging advanced scanning techniques and threat intelligence, Palo Alto enables organisations to proactively detect and remediate vulnerabilities before they can be exploited by malicious actors.
Key features of Palo Alto vulnerability management include:
- Vulnerability Scanning: Palo Alto conducts regular scans of your network to identify potential weaknesses in your systems and applications.
- Threat Intelligence: The platform utilises real-time threat intelligence to prioritise vulnerabilities based on their severity and the likelihood of exploitation.
- Automated Remediation: Palo Alto offers automated remediation options to quickly address identified vulnerabilities and reduce the risk of a security breach.
- Compliance Monitoring: The platform helps organisations ensure compliance with industry regulations and standards by identifying gaps in security controls.
By implementing Palo Alto vulnerability management, organisations can enhance their overall security posture, reduce the risk of data breaches, and protect sensitive information from cyber threats. With its user-friendly interface and powerful capabilities, Palo Alto provides a comprehensive solution for managing vulnerabilities across complex networks.
In conclusion, investing in Palo Alto vulnerability management is a proactive step towards safeguarding your organisation’s digital assets and maintaining a strong defence against cyber attacks. Stay ahead of emerging threats with Palo Alto Networks’ innovative approach to vulnerability management.
Top 5 Advantages of Palo Alto Vulnerability Management: Enhancing Network Security and Compliance
- Comprehensive vulnerability scanning to identify network weaknesses
- Real-time threat intelligence for prioritising vulnerabilities
- Automated remediation options for quick security fixes
- Helps ensure compliance with industry regulations and standards
- User-friendly interface and powerful capabilities
Challenges of Palo Alto Vulnerability Management: Costs, Complexity, and Compatibility Concerns
- High cost of implementation and maintenance.
- Steep learning curve for inexperienced users.
- Limited integration with third-party security tools.
- Resource-intensive scanning processes may impact network performance.
- Complexity of configuration settings can lead to misconfigurations and potential vulnerabilities.
- Lack of support for certain legacy systems or outdated software.
- Dependency on vendor updates for addressing newly discovered vulnerabilities.
Comprehensive vulnerability scanning to identify network weaknesses
Palo Alto vulnerability management offers a significant advantage through its comprehensive vulnerability scanning capabilities, which play a vital role in identifying network weaknesses. By conducting thorough scans of the network infrastructure, Palo Alto can pinpoint potential vulnerabilities in systems and applications, allowing organisations to take proactive measures to strengthen their security posture. This proactive approach enables businesses to address vulnerabilities before they can be exploited by cyber attackers, ultimately enhancing the overall resilience of the network and reducing the risk of security breaches.
Real-time threat intelligence for prioritising vulnerabilities
Palo Alto vulnerability management offers a significant advantage with its provision of real-time threat intelligence for prioritising vulnerabilities within a network. By leveraging up-to-date threat information, organisations can effectively identify and focus on addressing the most critical vulnerabilities that pose the highest risk of exploitation. This proactive approach enables businesses to stay one step ahead of cyber threats, enhancing their overall security posture and reducing the likelihood of successful attacks. With Palo Alto’s real-time threat intelligence capabilities, organisations can make informed decisions to strengthen their defences and mitigate potential security risks efficiently.
Automated remediation options for quick security fixes
One of the key advantages of Palo Alto vulnerability management is its automated remediation options, which offer quick and efficient security fixes. By automating the process of identifying and addressing vulnerabilities, organisations can significantly reduce the time and effort required to mitigate potential risks. This proactive approach not only enhances the overall security posture but also minimises the window of opportunity for cyber threats to exploit weaknesses in the network infrastructure. With Palo Alto’s automated remediation capabilities, organisations can swiftly respond to security issues, strengthen their defences, and maintain a resilient cybersecurity framework.
Helps ensure compliance with industry regulations and standards
Palo Alto vulnerability management plays a crucial role in helping organisations maintain compliance with industry regulations and standards. By identifying vulnerabilities and gaps in security controls, Palo Alto enables businesses to address potential non-compliance issues proactively. This proactive approach not only helps organisations avoid costly fines and penalties but also ensures that they uphold the necessary security measures to protect sensitive data and maintain trust with customers and stakeholders. With Palo Alto’s support, organisations can navigate the complex landscape of regulatory requirements with confidence and peace of mind.
User-friendly interface and powerful capabilities
Palo Alto vulnerability management stands out for its user-friendly interface and powerful capabilities, making it a top choice for organisations seeking an effective and efficient solution to safeguard their network infrastructure. The intuitive design of the platform allows users to navigate seamlessly through various features, while its robust capabilities empower them to identify, prioritise, and address security vulnerabilities with ease. This combination of user-friendliness and advanced functionality ensures that organisations can proactively manage their security posture without compromising on usability or effectiveness.
High cost of implementation and maintenance.
One significant drawback of Palo Alto vulnerability management is the high cost associated with its implementation and maintenance. The initial investment required to set up Palo Alto’s comprehensive security solutions can be substantial, making it challenging for smaller organisations with limited budgets to afford. Additionally, ongoing maintenance costs, including software updates, licensing fees, and support services, can further strain financial resources. This high cost of implementation and maintenance may deter some organisations from fully utilising Palo Alto vulnerability management, potentially leaving them vulnerable to cyber threats due to budget constraints.
Steep learning curve for inexperienced users.
For inexperienced users, one significant drawback of Palo Alto vulnerability management is the steep learning curve associated with the platform. Due to its advanced features and complex interface, new users may find it challenging to navigate and fully utilise the capabilities of Palo Alto effectively. The intricate configuration settings and technical terminology can be overwhelming for those without prior experience in cybersecurity, potentially leading to delays in implementing necessary security measures and optimising vulnerability management processes. Training and support resources may be required to help inexperienced users overcome this obstacle and maximise the benefits of Palo Alto vulnerability management.
Limited integration with third-party security tools.
One significant drawback of Palo Alto vulnerability management is its limited integration with third-party security tools. This lack of seamless compatibility with other security solutions may hinder organisations that rely on a diverse set of tools for their cybersecurity infrastructure. The restricted integration capability could result in inefficiencies in managing security operations, as well as potential gaps in threat detection and remediation processes. Organisations seeking a more holistic and interconnected approach to cybersecurity may find this limitation of Palo Alto vulnerability management challenging when aiming to achieve comprehensive protection across their network environment.
Resource-intensive scanning processes may impact network performance.
One notable drawback of Palo Alto vulnerability management is the potential impact on network performance due to resource-intensive scanning processes. As the platform conducts thorough scans to identify vulnerabilities across the network, it may consume significant resources, leading to a strain on network bandwidth and system resources. This could result in slower network speeds, increased latency, and potential disruptions to regular operations. Organisations considering Palo Alto vulnerability management should carefully assess their network infrastructure’s capacity to handle the scanning processes without compromising overall performance.
Complexity of configuration settings can lead to misconfigurations and potential vulnerabilities.
One notable drawback of Palo Alto vulnerability management is the complexity of its configuration settings, which can inadvertently lead to misconfigurations and potential vulnerabilities within the network infrastructure. The intricate nature of the platform’s settings may pose a challenge for users in correctly configuring and fine-tuning security parameters, increasing the risk of overlooking critical security measures or inadvertently exposing vulnerabilities. It is essential for organisations implementing Palo Alto vulnerability management to invest time and resources in training and regularly auditing configurations to mitigate the risk of misconfigurations that could compromise network security.
Lack of support for certain legacy systems or outdated software.
One significant drawback of Palo Alto vulnerability management is its lack of support for certain legacy systems or outdated software. This limitation can pose challenges for organisations that still rely on older technology or applications that are no longer actively supported. In such cases, the effectiveness of Palo Alto’s vulnerability management platform may be compromised, as it may struggle to accurately assess and address vulnerabilities within these unsupported systems. This gap in coverage highlights the importance of ensuring that all systems and software are up to date and compatible with the chosen cybersecurity solutions to maintain a robust security posture across the entire network infrastructure.
Dependency on vendor updates for addressing newly discovered vulnerabilities.
An inherent drawback of Palo Alto vulnerability management is the reliance on vendor updates to address newly discovered vulnerabilities. While Palo Alto Networks strives to provide timely patches and updates to mitigate security risks, the dependency on these updates can expose organisations to potential vulnerabilities during the lag time between identification and remediation. This delay in addressing emerging threats could leave systems vulnerable to exploitation by cyber attackers, highlighting the importance of proactive monitoring and supplementary security measures to bridge the gap between vulnerability detection and vendor-provided fixes.