Identity Management and Access Control in Cloud Computing
Cloud computing has revolutionised the way businesses operate, offering flexibility, scalability, and cost-efficiency. However, with this convenience comes the challenge of managing identities and controlling access to sensitive data stored in the cloud.
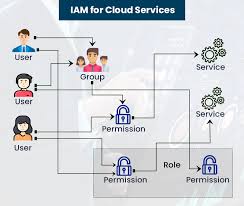
Identity management plays a crucial role in ensuring that only authorised individuals have access to cloud resources. It involves verifying users’ identities, granting appropriate permissions, and monitoring their activities to prevent unauthorised access.
Access control is another vital aspect of cloud security. It dictates who can access what information within a cloud environment. By implementing robust access control mechanisms, organisations can minimise the risk of data breaches and insider threats.
In cloud computing, identity management and access control work hand in hand to protect sensitive data from unauthorised access. Organisations can implement multi-factor authentication, role-based access control, and encryption to enhance security measures.
Effective identity management and access control not only safeguard data but also help organisations comply with regulatory requirements such as GDPR and HIPAA. By establishing clear policies and procedures for managing identities and controlling access, businesses can mitigate risks associated with storing data in the cloud.
In conclusion, identity management and access control are essential components of cloud security. By implementing robust practices and technologies in these areas, organisations can ensure the confidentiality, integrity, and availability of their data in the cloud.
9 Essential Tips for Effective Identity Management and Access Control in Cloud Computing
- Implement strong authentication methods such as multi-factor authentication.
- Regularly review and update user access permissions based on roles and responsibilities.
- Utilise encryption to protect sensitive data both in transit and at rest.
- Monitor user activity and set up alerts for any unusual behaviour or access patterns.
- Implement least privilege principle to restrict access to only what is necessary for each user.
- Use identity federation to enable single sign-on across different cloud services.
- Regularly audit access logs and conduct security assessments to identify potential vulnerabilities.
- Ensure proper offboarding procedures are in place when employees leave the organization to revoke their access promptly.
- Educate users about best practices for password management and security awareness training.
Implement strong authentication methods such as multi-factor authentication.
To enhance security in cloud computing, it is recommended to implement strong authentication methods such as multi-factor authentication. By requiring users to provide multiple forms of verification before accessing cloud resources, organisations can significantly reduce the risk of unauthorised access. Multi-factor authentication adds an extra layer of protection beyond traditional passwords, making it harder for malicious actors to compromise sensitive data stored in the cloud. This proactive approach to identity management and access control helps bolster overall cybersecurity measures and ensures that only authorised individuals can access critical information within a cloud environment.
Regularly review and update user access permissions based on roles and responsibilities.
In the realm of cloud computing security, it is imperative to regularly review and update user access permissions in alignment with their roles and responsibilities. By conducting periodic audits of user privileges and ensuring that access rights correspond accurately to job functions, organisations can bolster their defences against potential breaches and unauthorised activities. This proactive approach not only enhances data protection but also strengthens overall security posture in the ever-evolving landscape of cloud computing.
Utilise encryption to protect sensitive data both in transit and at rest.
To enhance security in cloud computing, it is advisable to utilise encryption to safeguard sensitive data both in transit and at rest. By encrypting data during transmission between devices and when stored on servers or databases, organisations can significantly reduce the risk of unauthorised access or interception. Encryption ensures that even if data is compromised, it remains unreadable without the corresponding decryption key, providing an additional layer of protection for valuable information in the cloud.
Monitor user activity and set up alerts for any unusual behaviour or access patterns.
Monitoring user activity and setting up alerts for any unusual behaviour or access patterns is a critical tip in identity management and access control in cloud computing. By actively monitoring how users interact with cloud resources, organisations can quickly detect potential security threats or breaches. Alerts for suspicious activities such as unauthorized access attempts or unusual data downloads can help IT teams respond promptly and mitigate risks before they escalate. This proactive approach enhances overall security posture and reinforces the protection of sensitive data stored in the cloud.
Implement least privilege principle to restrict access to only what is necessary for each user.
Implementing the least privilege principle in cloud computing is a fundamental strategy to enhance security and minimise risks. By restricting access to only what is necessary for each user, organisations can reduce the likelihood of data breaches and insider threats. This approach ensures that users have the minimum level of access required to perform their duties, thereby limiting the potential damage that could result from unauthorised actions. Embracing the least privilege principle not only strengthens identity management and access control but also contributes to a more secure and compliant cloud environment.
Use identity federation to enable single sign-on across different cloud services.
By utilising identity federation in cloud computing, organisations can streamline user authentication processes and enhance security by enabling single sign-on functionality across various cloud services. This approach allows users to access multiple cloud platforms with a single set of credentials, simplifying the user experience while maintaining strict control over access permissions. Identity federation promotes efficiency and convenience for users while ensuring that sensitive data remains protected across diverse cloud environments.
Regularly audit access logs and conduct security assessments to identify potential vulnerabilities.
To enhance security in cloud computing, it is advisable to regularly audit access logs and conduct security assessments. By reviewing access logs, organisations can track user activities and detect any suspicious behaviour that may indicate a security breach. Security assessments help identify potential vulnerabilities in the cloud environment, allowing for timely mitigation measures to be implemented. These proactive measures play a crucial role in maintaining the integrity and confidentiality of data stored in the cloud.
Ensure proper offboarding procedures are in place when employees leave the organization to revoke their access promptly.
In the realm of cloud computing security, it is imperative to establish proper offboarding procedures to swiftly revoke access when employees depart from the organisation. By promptly disabling access for former employees, organisations can mitigate the risk of unauthorised data breaches and maintain control over sensitive information stored in the cloud. Effective offboarding processes ensure that ex-employees no longer have access to confidential data, safeguarding the integrity of the organisation’s digital assets.
Educate users about best practices for password management and security awareness training.
Educating users about best practices for password management and providing security awareness training are crucial steps in enhancing identity management and access control in cloud computing. By promoting strong password policies, encouraging the use of unique and complex passwords, and regularly updating credentials, organisations can significantly reduce the risk of unauthorised access to sensitive data stored in the cloud. Security awareness training also plays a key role in empowering users to recognise potential threats, such as phishing attacks, and adopt secure behaviours when accessing cloud resources. By fostering a culture of security awareness among users, organisations can strengthen their overall cybersecurity posture in the cloud environment.