Privileged Identity Management in AWS
In the realm of cloud computing, Amazon Web Services (AWS) stands out as a leading provider of secure and scalable services. As businesses increasingly rely on AWS for their infrastructure needs, the importance of privileged identity management cannot be overstated.
Privileged identities refer to user accounts with elevated permissions that can access sensitive data and critical resources within an AWS environment. Managing these identities effectively is crucial for maintaining security and compliance standards.
With AWS Identity and Access Management (IAM), organisations can implement privileged identity management strategies to control and monitor access to their AWS resources. IAM allows for the creation of custom policies, role-based access controls, and multi-factor authentication to ensure that only authorised users have the necessary privileges.
By utilising IAM roles, organisations can assign temporary credentials to users or services, reducing the risk of long-term exposure of sensitive information. Additionally, IAM provides detailed logging and monitoring capabilities to track user activity and detect any suspicious behaviour.
Implementing privileged identity management in AWS is essential for preventing data breaches, insider threats, and unauthorised access to critical systems. By following best practices and leveraging the robust features of AWS IAM, organisations can enhance their security posture and protect their valuable assets in the cloud.
As businesses continue to embrace cloud technologies, prioritising privileged identity management in AWS will be key to safeguarding sensitive data and maintaining trust with customers. With a proactive approach to security and a comprehensive IAM strategy, organisations can confidently navigate the complexities of cloud computing while mitigating potential risks.
Understanding Privileged Identity Management (PIM) in AWS: Key Differences, Definitions, and Features
- Does AWS have PIM?
- What is the difference between IAM and privileged identity management?
- What is privileged identity access management?
- Is there PIM in AWS?
- What is privileged identity management?
- What’s the difference between PIM and Pam?
Does AWS have PIM?
One frequently asked question regarding privileged identity management in AWS is, “Does AWS have PIM?” The answer to this query lies in the robust capabilities of AWS Identity and Access Management (IAM), which serves as the foundation for managing privileged identities within the AWS environment. While AWS does not offer a standalone Privileged Identity Management (PIM) service, organisations can effectively implement PIM principles using IAM features such as custom policies, role-based access controls, and detailed monitoring. By leveraging IAM effectively, businesses can establish strong controls over privileged access and mitigate security risks in their AWS infrastructure.
What is the difference between IAM and privileged identity management?
When considering the distinction between IAM (Identity and Access Management) and privileged identity management in the context of AWS, it is important to understand their respective roles. IAM in AWS primarily focuses on managing user access to resources by defining permissions and policies. On the other hand, privileged identity management specifically deals with controlling and monitoring access to highly sensitive data and critical resources by users with elevated privileges. While IAM sets the foundation for access control within an AWS environment, privileged identity management goes a step further in safeguarding against potential security threats posed by users with elevated permissions. By implementing both IAM and privileged identity management practices effectively, organisations can establish a comprehensive security framework that addresses varying levels of access and ensures the protection of valuable assets in the cloud.
What is privileged identity access management?
Privileged Identity Access Management, often referred to as PIAM, is a crucial component of security measures within an AWS environment. It involves the management and control of user accounts with elevated permissions, known as privileged identities, to ensure that access to sensitive data and critical resources is restricted to authorised individuals only. By implementing PIAM practices in AWS, organisations can enforce strict access controls, monitor user activity effectively, and mitigate the risk of data breaches or unauthorised access. Prioritising privileged identity access management is essential for maintaining the integrity and security of an AWS infrastructure, safeguarding valuable assets from potential threats.
Is there PIM in AWS?
Privileged Identity Management (PIM) plays a critical role in ensuring secure access to sensitive resources within Amazon Web Services (AWS). While AWS does not have a specific service called “PIM,” organisations can effectively implement privileged identity management strategies using AWS Identity and Access Management (IAM). IAM allows users to define and manage user permissions, roles, and policies to control access to AWS resources. By leveraging IAM features such as role-based access controls and multi-factor authentication, organisations can establish robust PIM practices within their AWS environments to safeguard against unauthorised access and potential security risks.
What is privileged identity management?
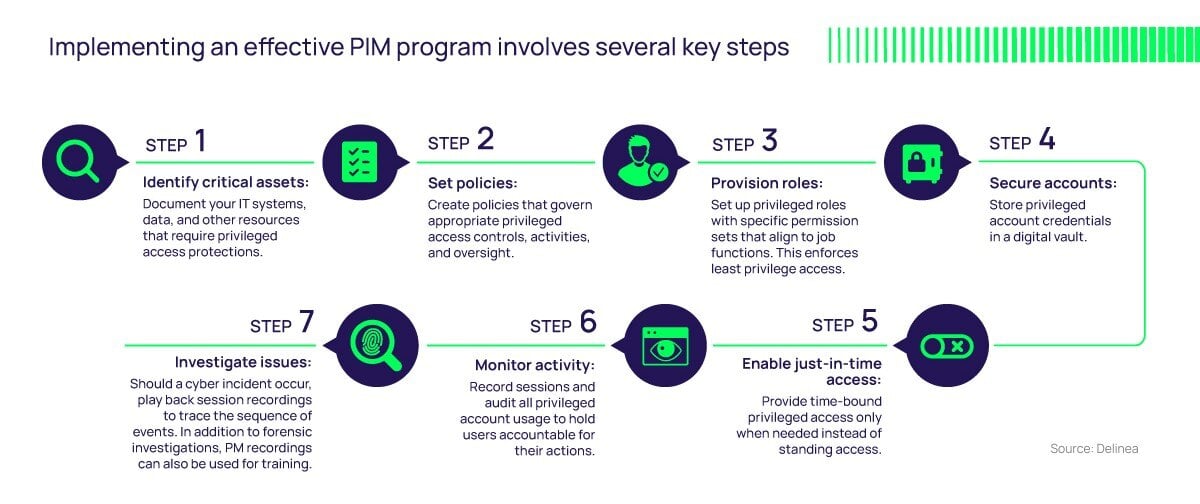
Privileged Identity Management (PIM) in the context of Amazon Web Services (AWS) refers to the practice of managing user accounts with elevated permissions that have access to sensitive data and critical resources within an AWS environment. PIM involves implementing strategies and controls to ensure that only authorised users have the necessary privileges to perform specific actions, reducing the risk of data breaches and unauthorised access. By using AWS Identity and Access Management (IAM) features such as custom policies, role-based access controls, and monitoring capabilities, organisations can effectively govern and secure their privileged identities in compliance with security best practices.
What’s the difference between PIM and Pam?
When discussing privileged identity management in AWS, a commonly asked question is about the distinction between PIM (Privileged Identity Management) and PAM (Privileged Access Management). While both concepts focus on managing and securing privileged accounts within an environment, they serve different purposes. PIM typically refers to the overall process of managing and controlling access to privileged identities, including monitoring user activity and enforcing security policies. On the other hand, PAM specifically deals with managing the lifecycle of privileged access, such as granting temporary permissions, rotating credentials, and enforcing least privilege principles. Understanding the nuances between PIM and PAM is crucial for implementing a comprehensive privileged identity management strategy in AWS that effectively safeguards sensitive data and critical resources.